Using fail2ban to secure your server
Last week I logged into my VPS with SSH for the first time in 2 weeks and got this message:
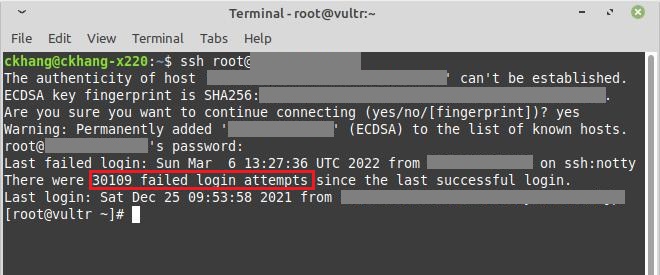 30109 failed login attempts! For a VPS with public IP with an exposed ssh port, that’s pretty low, according to some people on /r/sysadmin/ (my favorite subreddit!). But I’m still decided to add some protection to the server. After some simple research, fail2ban seems to be the solution.
30109 failed login attempts! For a VPS with public IP with an exposed ssh port, that’s pretty low, according to some people on /r/sysadmin/ (my favorite subreddit!). But I’m still decided to add some protection to the server. After some simple research, fail2ban seems to be the solution.
Fail2ban is an application that monitors system logs for symptoms of an attack on your server, written in python.
While Fail2ban is primarily focused on SSH attacks, you can also use Fail2ban configuration with other services that utilize log files and is at potential risk of being compromised.
Installing
Fail2ban is not available in the official CentOS package repository, so I have to install the EPEL repository:
|
|
Then install fail2ban:
|
|
Enable fail2ban using systemctl:
|
|
Configuring
fail2ban config files are stored in /etc/fail2ban directory:
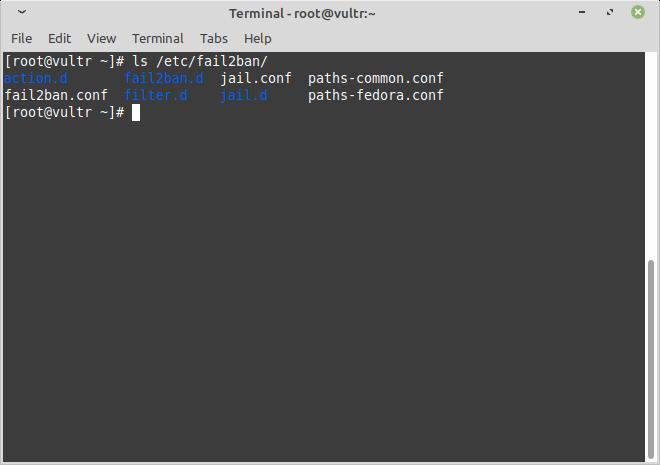 Default config file is
Default config file is jail.conf, but I should avoid editing it directly since it may be overwritten when upgrading package. Since fail2ban reads .conf configuration files first, then .local files override any setting, I will create a new jail.local.
|
|
(feel free to use other text editor, here I used nano)
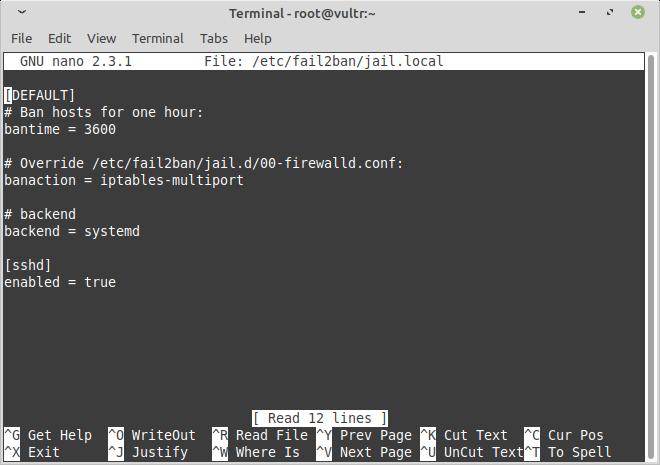
Here I defined some basic value. Also, in case of CentOS or Fedora, I need to change the backend option in jail.local from auto to systemd.
Restart fail2ban to apply the changes:
|
|
Running
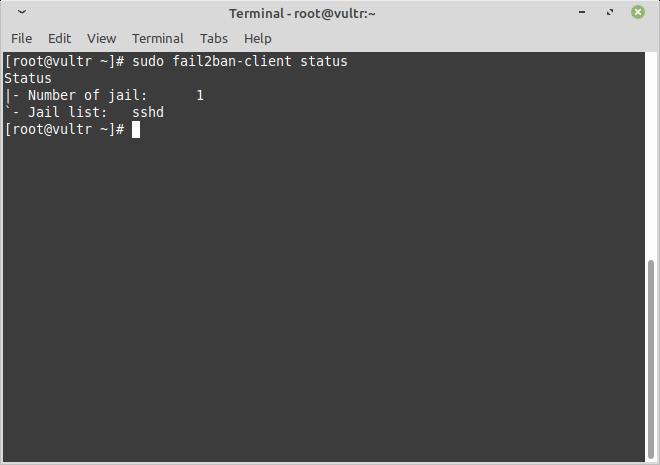
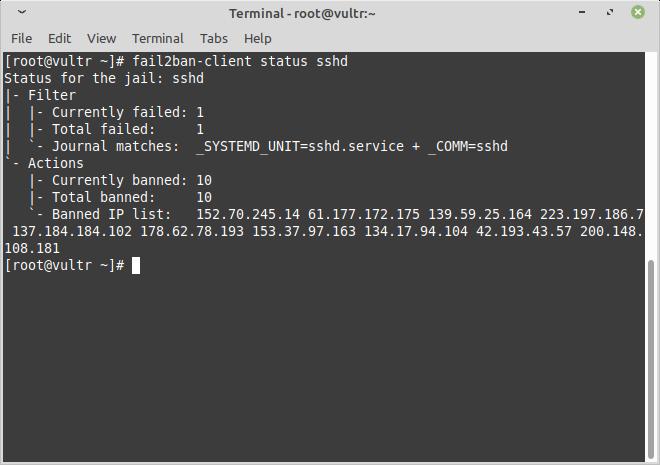
I can check for fail2ban client status by using:
|
|
 To get more information on ssh jail:
To get more information on ssh jail:
|
|
Other options
This is just the basic to get started with fail2ban. There are many things you can explore like mail notifications, filters, regex etc.
References: